Handala Hacks FBI Director Kash Patel's Personal Email; DOJ Seizes Four Iranian Cyber Influence Domains
Source: X
EXECUTIVE SUMMARY
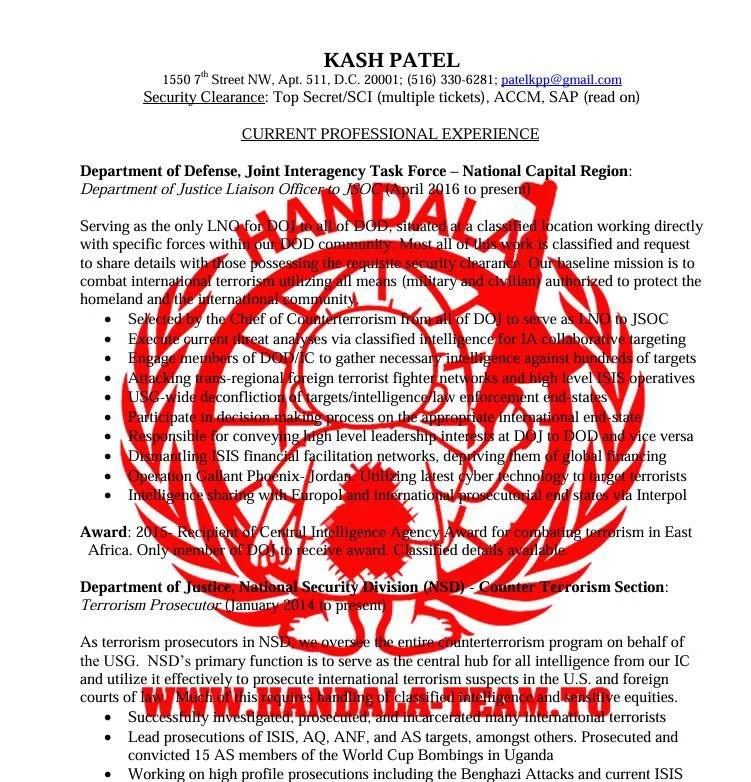
The IRGC Ministry of Intelligence-affiliated Handala hacking group breached FBI Director Kash Patel's personal Gmail account on or before March 27, publishing personal photos and years of correspondence online. The breach was confirmed authentic by a Justice Department official. On the same day, the FBI seized four Handala-operated domains as part of a broader disruption of Iranian cyber-enabled psychological operations.
ANALYSIS
The Patel breach represents a significant escalation in Iran's cyber campaign against US law enforcement leadership. Handala published photographs of Patel alongside what appear to be Cuban license plates and cigars, apparently intended to embarrass, and linked to a cache of emails dating from approximately 2011 to 2022. The FBI stated the material is historical and contains no government information, limiting operational damage. However, the targeting of the sitting FBI director personally, and the rapid confirmation of the breach's authenticity by DOJ, carries significant counterintelligence implications: it demonstrates that Iran-linked actors held personal digital access to a high-ranking US law enforcement figure for an extended period.
The timing and motivation are explicit. Handala publicly stated this was retaliation for the FBI's seizure of several Handala domains, which itself followed Handala's earlier claim of responsibility for wiping over 200,000 Stryker medical devices via Microsoft Intune. This creates an escalating tit-for-tat cycle: US government action triggers Iranian counter-action targeting the US official who authorized it. The Trump administration is offering a $10 million reward for information identifying Handala group members, indicating the FBI has not yet attributed individual identities within the group.
Concurrently, the DOJ announced the seizure of four additional domains as part of a broader disruption of Iranian Cyber Enabled Psychological Operations. Handala's rapid counter-response, posting within hours of the domain seizure, suggests the group maintains redundant infrastructure and communication channels that allow near-real-time operational response. The convergence of the domain seizure and the Patel breach on the same day suggests pre-positioned access to Patel's account was held in reserve as a deterrence or retaliation asset. The DHS partial shutdown, now in its sixth week, continues to constrain the US government's coordinated cyber defense posture at precisely the moment Iran's cyber tempo is at its highest.
SOURCES
Axios: Iran-linked group claims hack of FBI Director Kash Patel
TechCrunch: Iranian hackers claim breach of FBI director Kash Patel's personal email account
CNBC: Iran-linked hackers breach FBI Director Kash Patel's personal email
CBS News: FBI Director Kash Patel's personal email breached by hackers linked to Iran
Telegram/Bellum Acta (Handala domain seizure + breach claim, primary collection)
Telegram/WarCabinet (WarCabinet Handala-Patel breach corroboration)