Russia Providing Satellite Intelligence and Cyber Support to Iran to Target US Bases, Ukrainian Assessment Reveals
EXECUTIVE SUMMARY
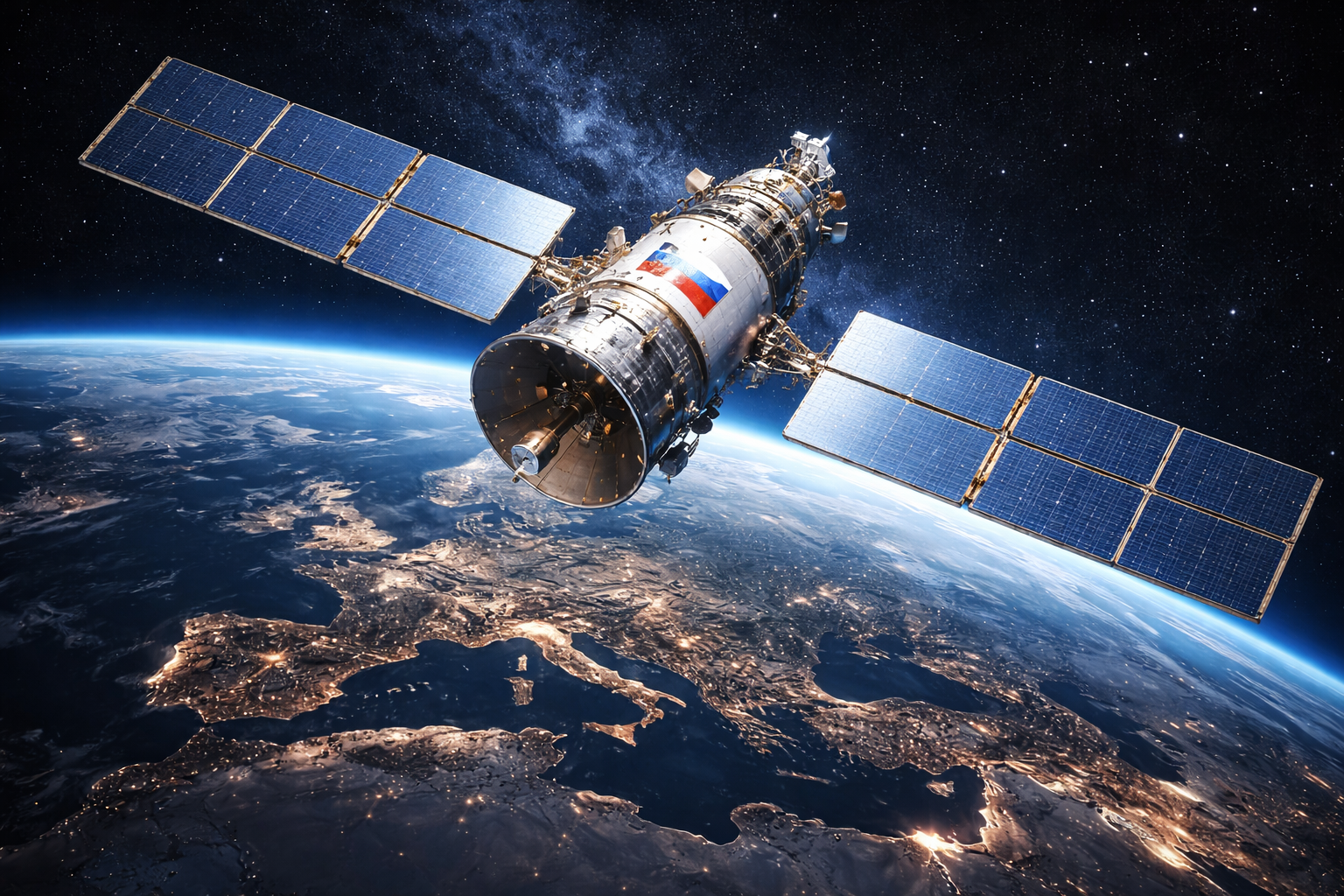
Ukrainian military intelligence shared an assessment with Reuters on April 7 revealing that Russian satellites conducted at least 24 detailed surveillance surveys of 46 targets across 11 Middle Eastern countries between March 21 and 31, and that this imagery was shared with Iran to enable targeting of US and allied military installations. A Western military source and a regional security source separately confirmed Russian satellite activity in the region and imagery sharing with Iran. The assessment also documents collaboration between Russian hacker groups and Iran's Handala Hack cyber unit in targeting Gulf-region critical infrastructure and telecommunications.
ANALYSIS
The most operationally significant detail in the Ukrainian assessment is the targeted surveillance of King Khalid Military City in Saudi Arabia, specifically five surveys aimed at locating elements of the US-made THAAD air defense system deployed there. THAAD is the highest-tier missile defense asset in theater; identifying its precise location and orientation enables Iran to calibrate ballistic missile trajectories to avoid or saturate it. This represents Russian intelligence directly enabling attacks on US air defense infrastructure protecting US forces and Saudi Arabian facilities.
The pattern the assessment describes, with surveyed sites subsequently struck by Iranian missiles and drones within days, implies near-real-time intelligence sharing rather than archival data transfer. This is a qualitative escalation in Russian support for Iran. Russia has consistently denied providing lethal support to Iran during the conflict; providing precise targeting intelligence for strikes on US bases is functionally equivalent to active participation in attacks on US forces.
The cyber collaboration dimension adds another vector. Russian hacker groups Z-Pentest Alliance, NoName057(16), and DDoSia Project interacting with Iran's Handala Hack creates a combined capability that blends Iranian regional knowledge with Russian technical depth. Handala has already been associated with attacks on Gulf infrastructure; Russian amplification of that capability increases both the scale and sophistication of what Iran can execute. Gulf-region critical infrastructure sectors, particularly telecommunications and energy management systems, face elevated threat from this hybrid collaboration.
For US domestic cybersecurity, the Handala-Russian collaboration is directly relevant to CISA's threat picture. Handala has previously claimed attacks on Israeli and Gulf-adjacent targets; the introduction of Russian technical collaboration increases the risk that Handala operations could extend to continental US networks, particularly in sectors with Middle East business exposure. DHS should assess whether the collaboration has extended to US-facing infrastructure reconnaissance.
SOURCES
Defense News: Russia supplies Iran with cyber support, spy imagery to hone attacks, Ukraine says
Japan Times: Russian satellite imagery used by Iran to target U.S. forces, Ukraine reports
OSINT Navigator: CENTCOM commander confirms hundreds of US drones involved in Iran war (DefenseScoop, April 7)